“Fraud detection solutions need not only to prevent fraud, but also need to deliver a superior experience to the end-consumer.”
That was the takeaway in the discussion about striking a balance between fraud and customer experience. But how do you optimize risk models? Existing models tend to take on typical customer information such as name, phone number, address, and email. What else is needed?
Dynamic Identity Elements
There are many ways to verify a customer. Measures can be put into place by asking more questions, double checking, and triple checking their identity. However, these tactics typically inconvenience the customer and do not translate to a good experience.
In making a purchase, customer data points such as name, phone, address and email are typically provided. Oftentimes a fifth attribute, IP address, is also captured. These data points are gathered and assessed for validity to keep customer friction to a minimum. Rather than asking the customer about their pet’s name or their favorite ice cream flavor, machine learning can be utilized to see patterns in data, ensuring the customer is who they said they are. It is not rocket science, but it is science.
Looking at the five aforementioned attributes, we must look beyond their face value. Rather than just looking at them individually, look at them holistically – their relationships and history. Has Tim Taylor always lived at 123 Main Street in Detroit, Michigan? If not, how long has he resided there? Where else did he live? Is there a link between his name and the phone number? If there is not a correlation between his phone and current address, is there one between the phone and former address? There are many ways to find correlations and to flag anomalies in assessing the validity of a customer.
There is more intelligence that could offer additional insights on the customer. Tim recently made a large purchase at an online music outlet. The purchase was an anomaly, as he is typically a heavy home improvement consumer. We know Tim’s online transaction behavior through tracking transactions throughout a vast network of businesses globally. But what does this mean for Tim and the online music outlet? Is it a fraudulent transaction or is Tim starting a band? The answer is still uncertain, but that answer in itself is important.
Predictive Risk Scores
Existing fraud models that rely on static data points to verify an identity may be too one-dimensional. They are able to assess, to some extent, the validity of a transaction, but machine-learning models complement these rules for more accurate results.
The Ekata platform hosts highly predictive signals to help differentiate good customers from fraudsters. The Ekata Identity Engine returns two specific responses that predict risk levels – Confidence Score and Identity Network Score.
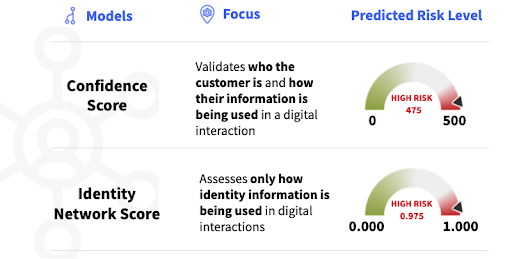
For Tim’s transaction at the online music outlet, if it was assessed on the Ekata platform and the resulting signals show a Confidence Score of 475 and an Identity Network Score of 0.975, then the probability that it is a fraudulent transaction is high. On the contrary, if it shows a Confidence Score of 150 and an Identity Network Score of 0.400, then the fact that Tim is starting a band may not be a far-fetched idea.
Solving the Problem at Scale
Tim, a legitimate customer, is just one of many legitimate customers for whom this merchant rejects. But in that pool of rejections, there is a large percentage of bad actors who are trying to use fraudulent information to obtain goods. How can the merchant know who is good and who is bad when a transaction is rejected? After all, there was a legitimate reason to reject in the first place.
The answer is surprisingly simple: look at transactions where the outcome is known, i.e., accepted transactions that resulted in fraud or not. For mature fraud models, there is probably no difference, but by bringing in features from third party data, we can get a new view on these transactions.
The image below is an example of such a comparison. What you are seeing is a heat map comparing Confidence Score on the horizontal axis with Identity Network Score on the vertical axis for good (green) and bad (red) transactions.
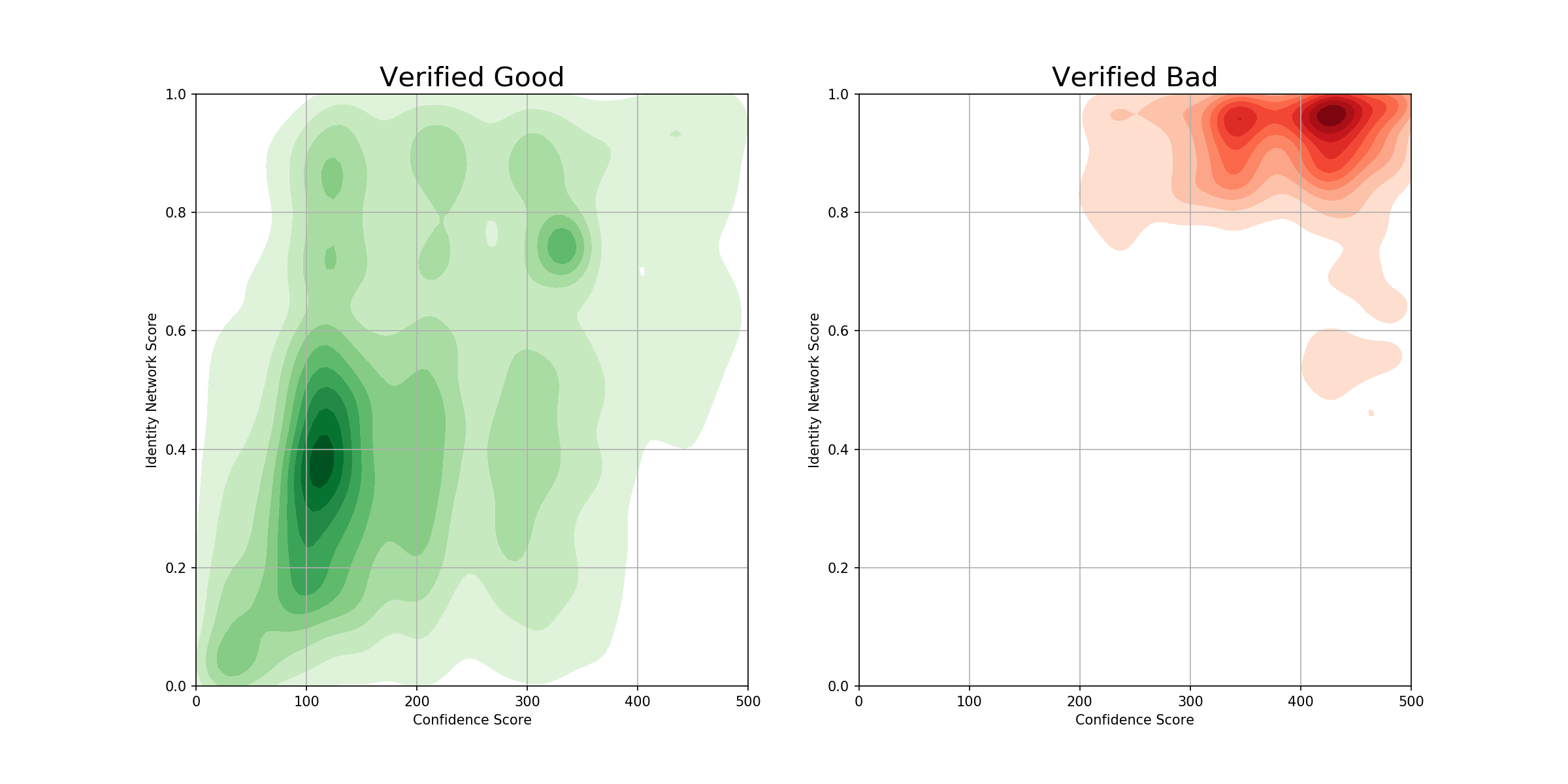
The comparison of good and bad transactions can be used to draw dividing lines when deciding to accept transactions that were previously rejected. Below is the same heatmap for transactions that were rejected. Notice that it looks a lot like we sampled from the good and bad transactions almost at random. Based on our learnings from the green and red heatmaps, we can deduce the lowest risk population to consider accepting.
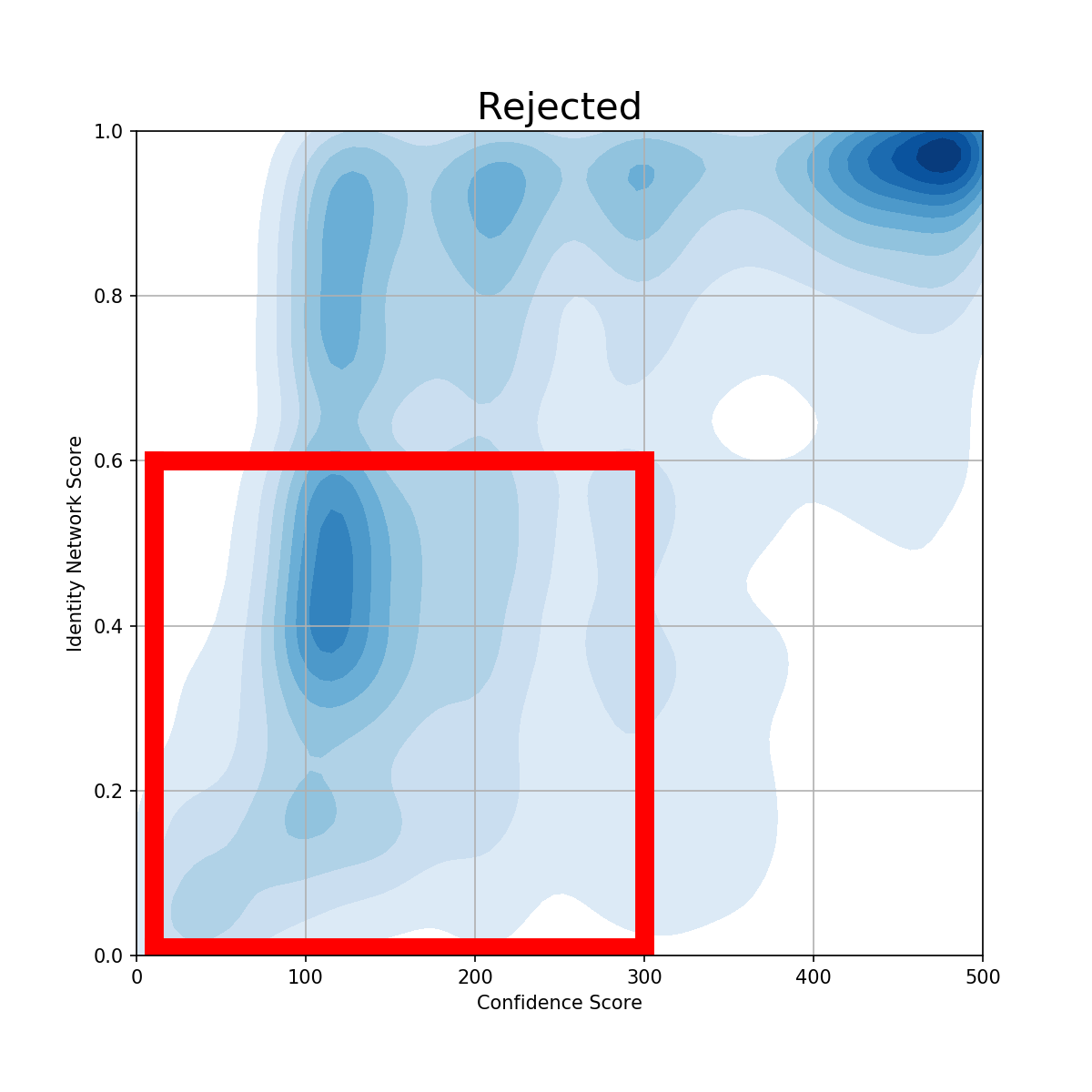
In the example on the right, we look at the population of all rejected transactions. We draw lines at Confidence Score of < 300 and Identity Network Score of < 0.6, which includes 40% of all rejects, but a population that only has 1% of the fraud rate of known transactions.
Using Confidence Score and Identity Network Score together, the merchant can begin to implement this on future transactions. In doing so, it will capture fraudulent transactions as it always has but will, at the same time, allow more legitimate transactions through in a mindful and calculated way.
For more information on false declines and how to identify and prevent them, download our ebook, Reducing False Declines: How to Identify and Keep Good Customers.



